The History and Evolution of Passkeys: From Passwords to Passwordless
A brief into the history and evolution of passkeys, tracing their journey from inception to their current state and future prospects.

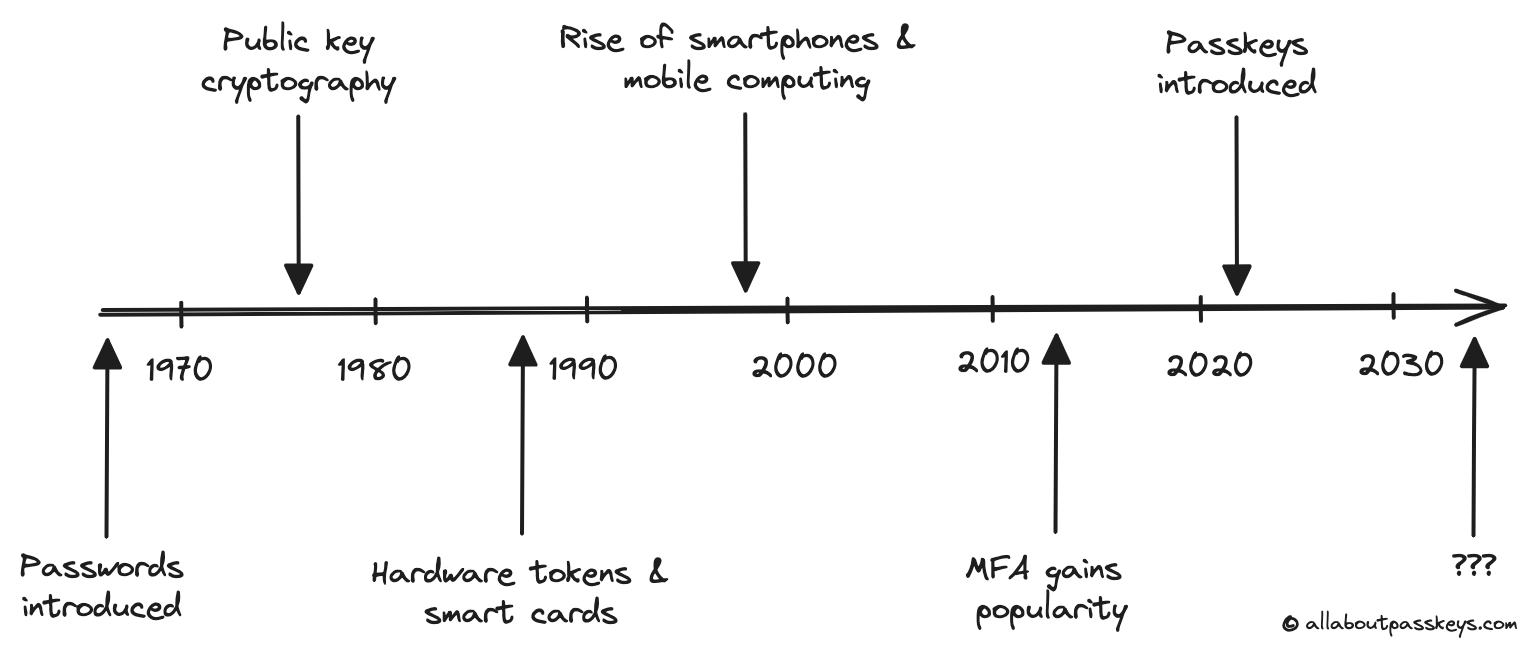
For over 60 years, passwords have been the default method of online authentication, with security researchers continually seeking to replace them with more secure alternatives like passkeys. Passkeys are the culmination of that effort. But to understand why passkeys matter, it helps to trace how we got here.
The Problem Passkeys Were Built to Solve
Traditional passwords have a fundamental design flaw: they are shared secrets. When you create a password, a version of it is stored on the server. That means every database breach, every phishing page, every keylogger represents a real threat to your credentials. Add to that the human tendency to reuse passwords, choose weak ones, and forget them entirely — and it becomes clear that the problem isn't just implementation. The architecture itself is broken.
Passkeys were developed specifically to eliminate shared secrets from the authentication equation. As we covered in What are passkeys and how do they work?, they replace passwords with cryptographic key pairs — a public key stored on the server, and a private key that never leaves your device. But this idea didn't emerge overnight.
The Origins: Public Key Cryptography (1970s)
In 1976, Whitfield Diffie and Martin Hellman published a landmark paper on public key cryptography, laying the intellectual foundation for passkeys and modern authentication methods. Their insight — that two parties could establish secure communication without ever sharing a secret — was revolutionary. For the first time, it became theoretically possible to prove your identity to a server without transmitting anything an attacker could use. This asymmetric encryption model is the direct ancestor of how passkeys work today. The private key proves identity; the public key verifies it. Nothing sensitive crosses the network.
Early Implementations: Hardware Tokens and Smart Cards (1980s–2000s)
Through the 1980s and 1990s, organisations began exploring physical alternatives to passwords. Hardware tokens — small devices that generated time-based one-time codes — added a second factor to authentication. Smart cards took this further, embedding cryptographic keys in a physical card that users would insert into a reader.
These solutions worked, and they were genuinely more secure than passwords alone. But they failed to scale. Carrying a separate device was inconvenient for everyday users, expensive for organisations to deploy and manage, and entirely impractical for consumer internet use. Security without usability doesn't get adopted — a lesson that would shape everything that followed.
The Smartphone Era Changes Everything (2000s–2010s)
The widespread adoption of smartphones in the late 2000s presented a new opportunity for the development and implementation of passkeys. For the first time, billions of people were carrying a powerful personal computer equipped with a secure processor, biometric sensors, and always-on connectivity. The phone became both the authentication device and the user interface — solving the hardware token's portability problem in one stroke.
This period also saw the rise of biometric authentication — fingerprint readers on the iPhone 5S in 2013, then Face ID in 2017 — normalising the idea that a device could verify your identity without a password. These weren't passkeys yet, but they established the user behaviour that passkeys would later build on.
The FIDO Alliance and the Standardisation of Passkeys (2012–2018)
The critical institutional moment came in 2012, with the formation of the FIDO (Fast Identity Online) Alliance. Founded by PayPal, Lenovo, and a group of security companies, FIDO set out to solve the standards problem — the reason every hardware token, smart card, and proprietary system had failed to achieve universal adoption.
FIDO's first major output was U2F (Universal 2nd Factor) in 2014, a standard that allowed hardware security keys to work as a second factor across any supporting site. Google was an early adopter, and the results were striking — phishing attacks on Google employee accounts dropped to zero after U2F deployment.
But U2F still required a password as the first factor. The bigger leap came with FIDO2, launched in 2018 in partnership with the W3C. FIDO2 introduced WebAuthn — the browser API that enables passkey authentication on the web — and CTAP2, which extended support to external authenticators. For the first time, a fully passwordless login standard existed that was open, cross-platform, and backed by the major browser vendors. We cover the technical details of WebAuthn in WebAuthn: The Backbone of Modern Passkey Authentication.
The Major Platform Commitment (2022–Present)
Although FIDO2 and WebAuthn had been around for several years, they gained mainstream recognition in 2022 when major platforms committed to supporting passkeys. A significant turning point came in May 2022, when Apple, Google, and Microsoft jointly announced expanded support for FIDO2 passkeys across their platforms, marking a major milestone in the adoption of passwordless authentication. This wasn't just technical support — it was a coordinated public commitment that passkeys would be built into iOS, Android, macOS, Windows, Chrome, and Safari as first-class features. This widespread adoption by industry leaders marked a turning point, signalling the beginning of a new era in authentication where passkeys could potentially replace traditional passwords on a global scale.
Where Passkeys Are Headed
The trajectory is clear: passkeys are becoming the default authentication method for consumer and enterprise applications alike. Several developments will shape the next phase:
- Enterprise adoption is accelerating, with identity providers like Microsoft Entra and Okta integrating passkey support — something we explore in [Passkeys in the enterprise: Challenges and strategies for large-scale adoption]
- Cross-device passkey management is maturing, with synced passkeys via iCloud Keychain and Google Password Manager making device loss far less disruptive
- Regulatory pressure is increasing in sectors like finance and healthcare, where passwordless authentication aligns with data protection requirements
- Quantum computing presents a longer-term consideration for the cryptographic algorithms underlying passkeys — a topic we'll examine in [The role of quantum computing in the evolution of passkey cryptography]
The 50-year journey from Diffie and Hellman's paper to a passkey on your iPhone is a story of good ideas waiting for the right infrastructure. That infrastructure now exists.